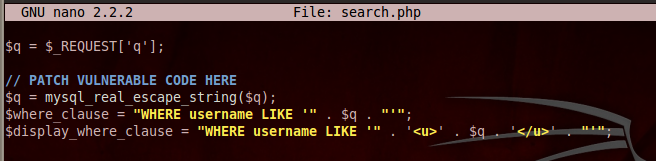
6. Challenges
Use the forms above to inject usernames that do the things below.
Capture FULL SCREEN images of each challenge when you have
completed it.
For hints, see the "Sources" at the bottom of the page.
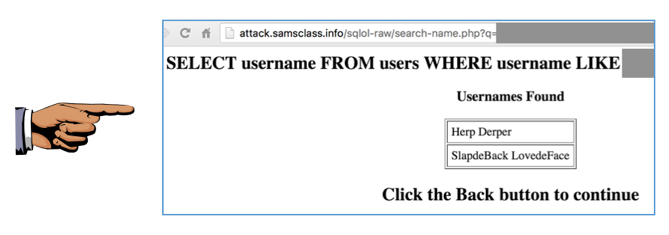
Challenge 1: Display names for administrators only,
as shown below. (5 pts.)
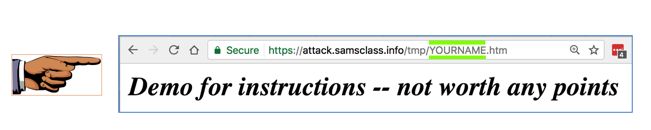
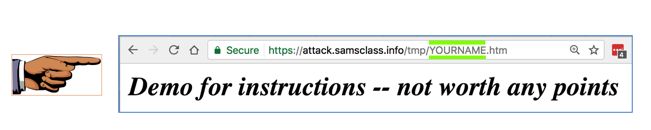
Challenge 2: Create a file on my server with your name as a filename,
as shown below. (5 pts.)
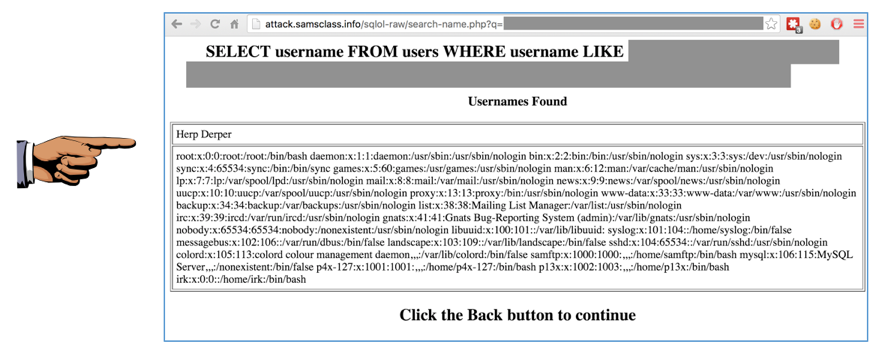
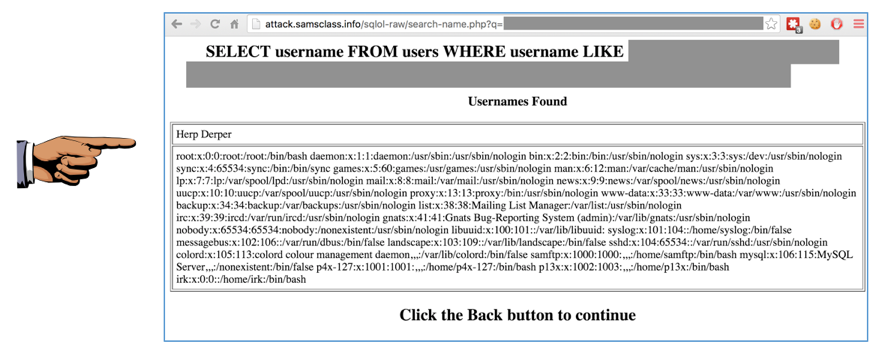
Challenge 3: Display the /etc/passwd file in a browser,
as shown below (5 pts.)
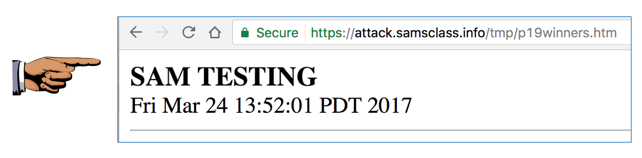
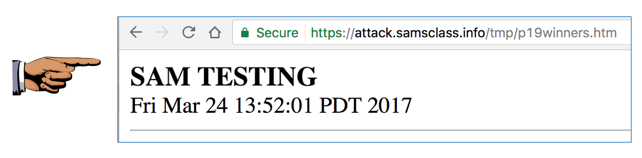
Challenge 4: Put your name into this file. (5 pts.)
/tmp/p19winner
Within a minute, your name will appear on
the
Winners page
as shown below:
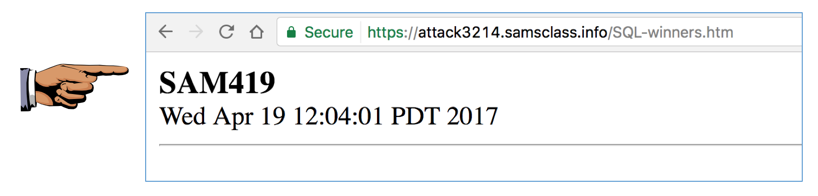
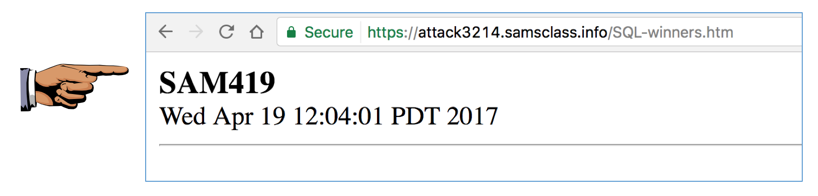
Challenge 5: Get onto the Winners page. (10 pts. extra credit)
Use a different server, without the
option to use raw SELECT queries.
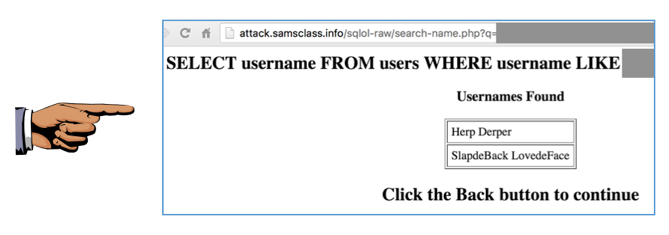
Before starting, click the button below
to reset the database:
Now use this name search form:
Put your name into these two files on that server:
/tmp/SQLchal/winners
/tmp/SQLchal/updatenow
Within a minute, your name will appear on the
Winners
page as shown below:
Hint
Start by uploading a PHP shell to the server. Then use
that shell to complete the task.
|
|